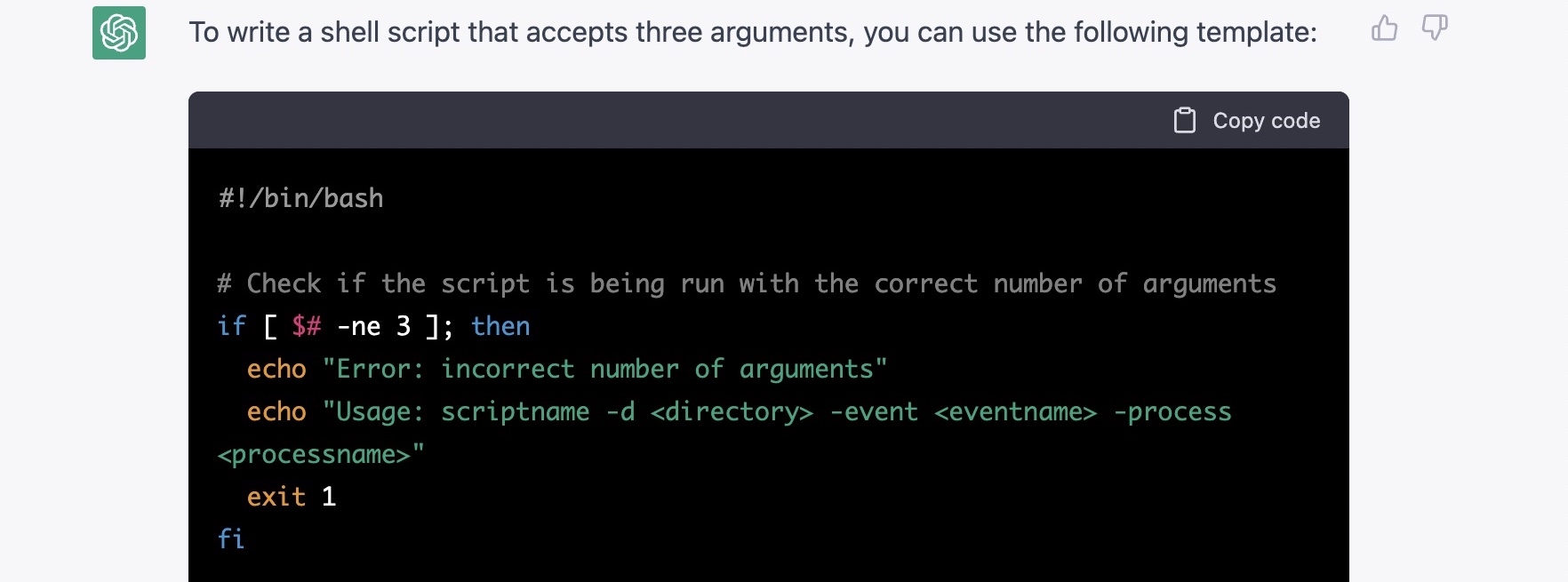
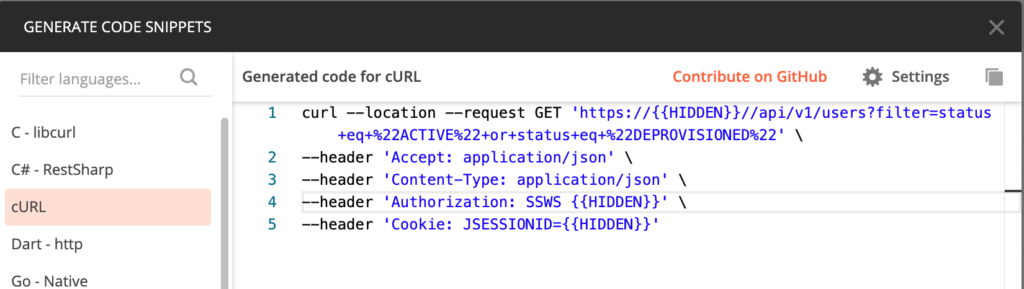
By now, ChatGPT has become pretty well known ( as of 18th Dec 2022). I’ve messed around with basic questions, but today I wanted to start to write a script that I could use with “OverSight” on Mac (https://objective-see.org/products/oversight.html). When you turn on your camera/mic, it can fire off a script with arguments.
In this post I’ll show you what I asked ChatGPT, what it gave me and if it worked! And if Google helped me or not, and if learning to code (or just knowing logic), is still worthwhile.
Continue reading “I asked ChatGPT to write me a bash script, and it worked (mostly), why do I need to know how to code?”